How to Create a Conditional Access Policy in Microsoft Entra
Conditional Access policies in Microsoft Entra allow administrators to control access to applications and resources based on specific conditions.
By creating these policies, organizations can enforce security measures such as Multi-Factor Authentication (MFA), device compliance, and location-based access control.
2 Ways of Creating Conditional Access Policy
Administrators can create Conditional Access policies using:
- Microsoft Entra Admin Center (GUI)
- Microsoft Graph PowerShell (automation)
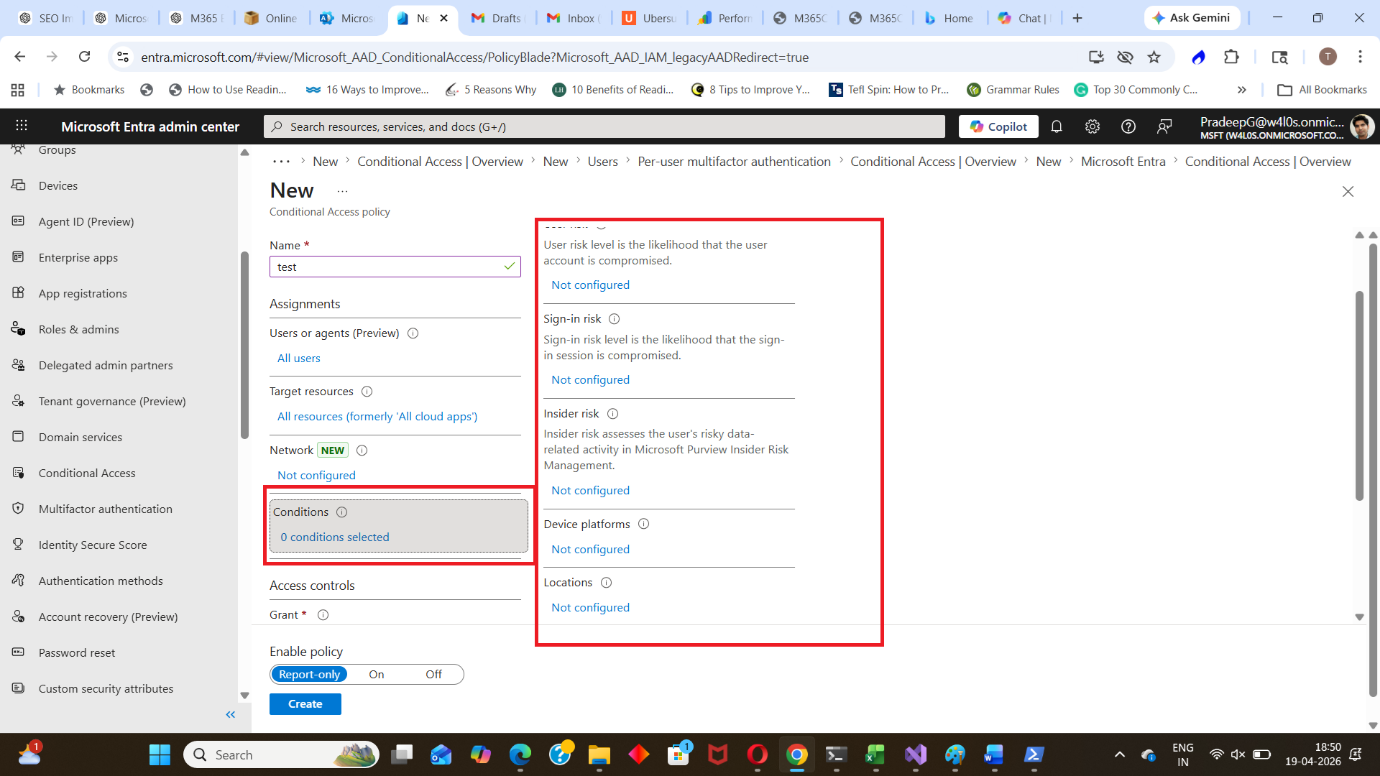
Create a Conditional Access Policy Using the Entra Admin Center
Follow these steps to create a policy.
- Go to the Microsoft Entra Admin Center: https://entra.microsoft.com
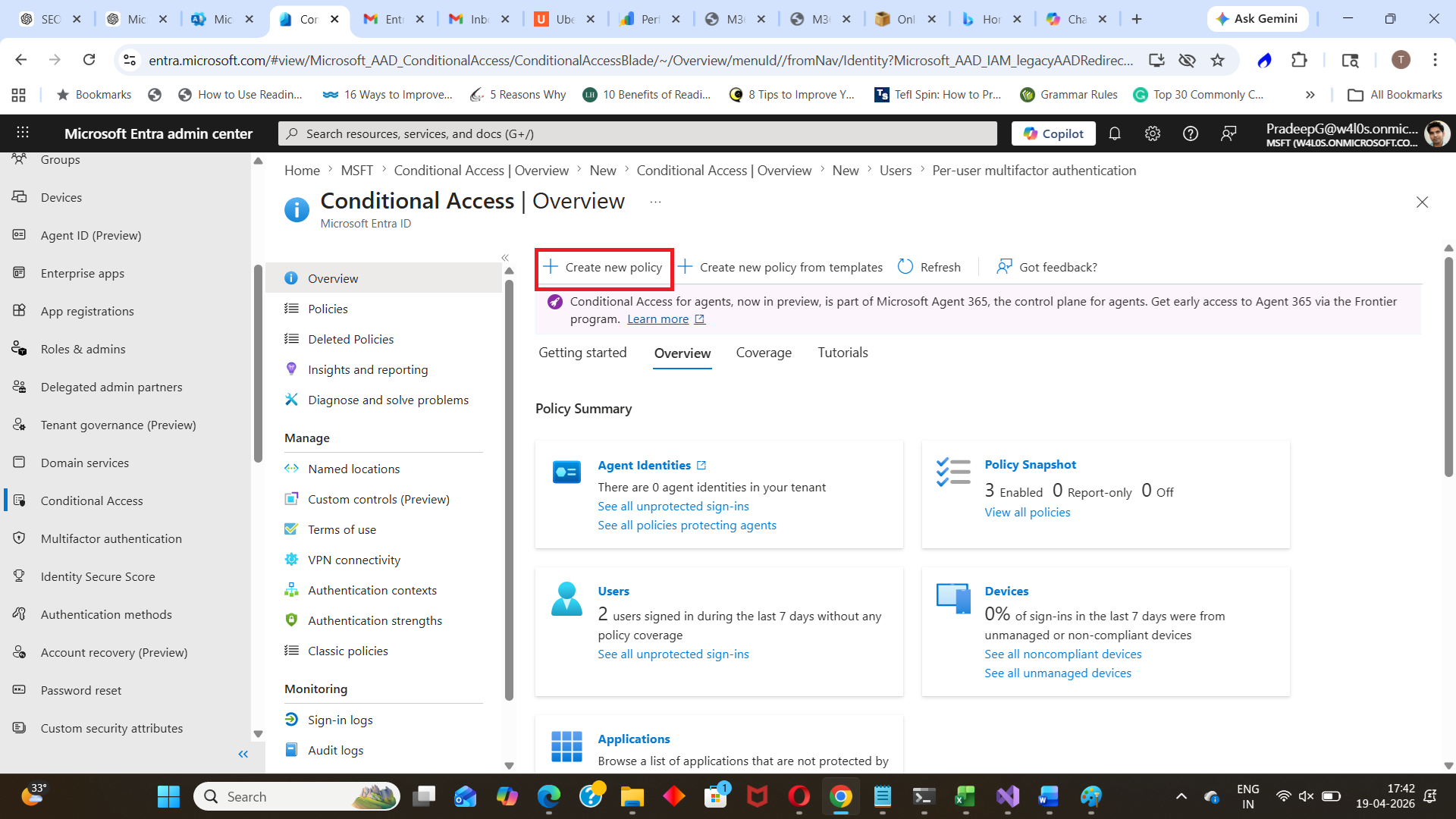
- Navigate to: Microsoft Entra ID → Conditional Access
- Click New policy
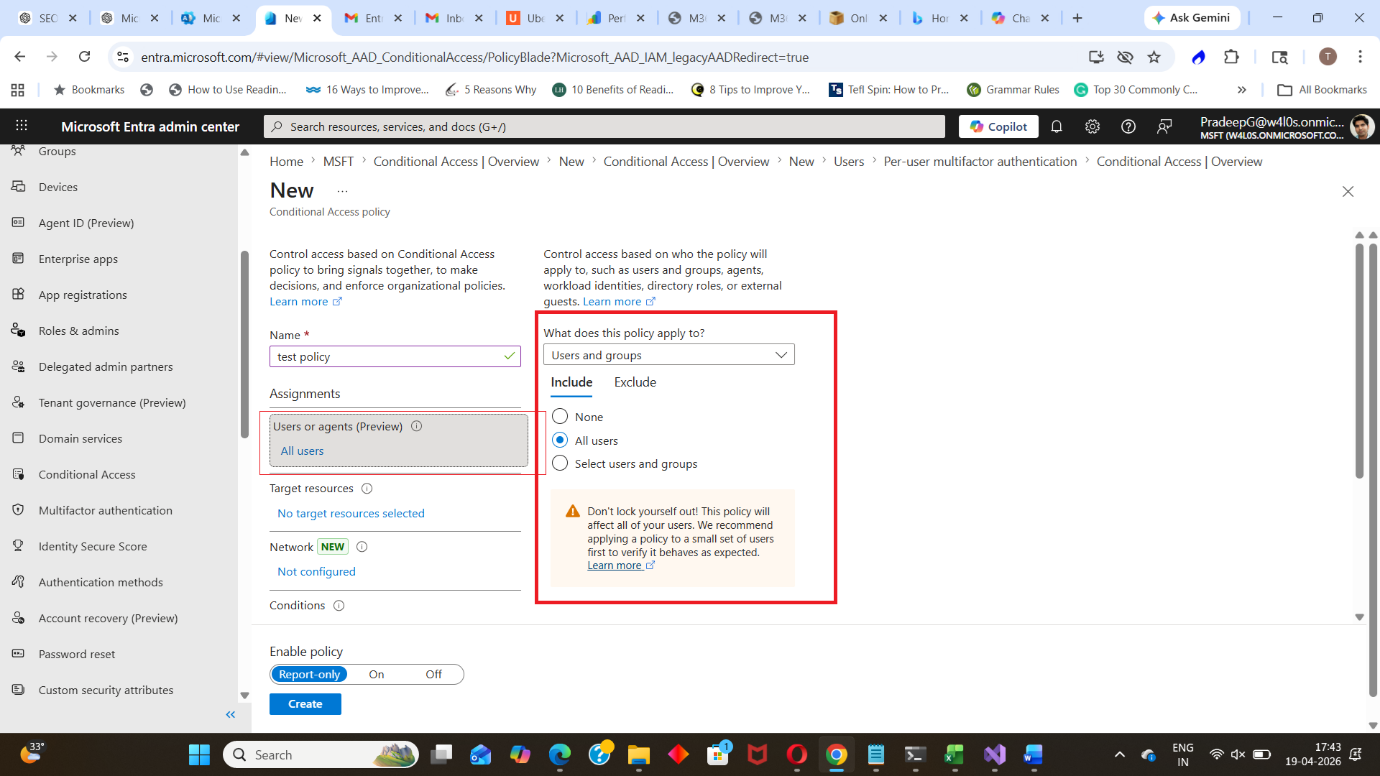
- Provide a name for the policy. Example: Require MFA for External Access
- Configure Assignments
-
All users
or - Specific users/groups
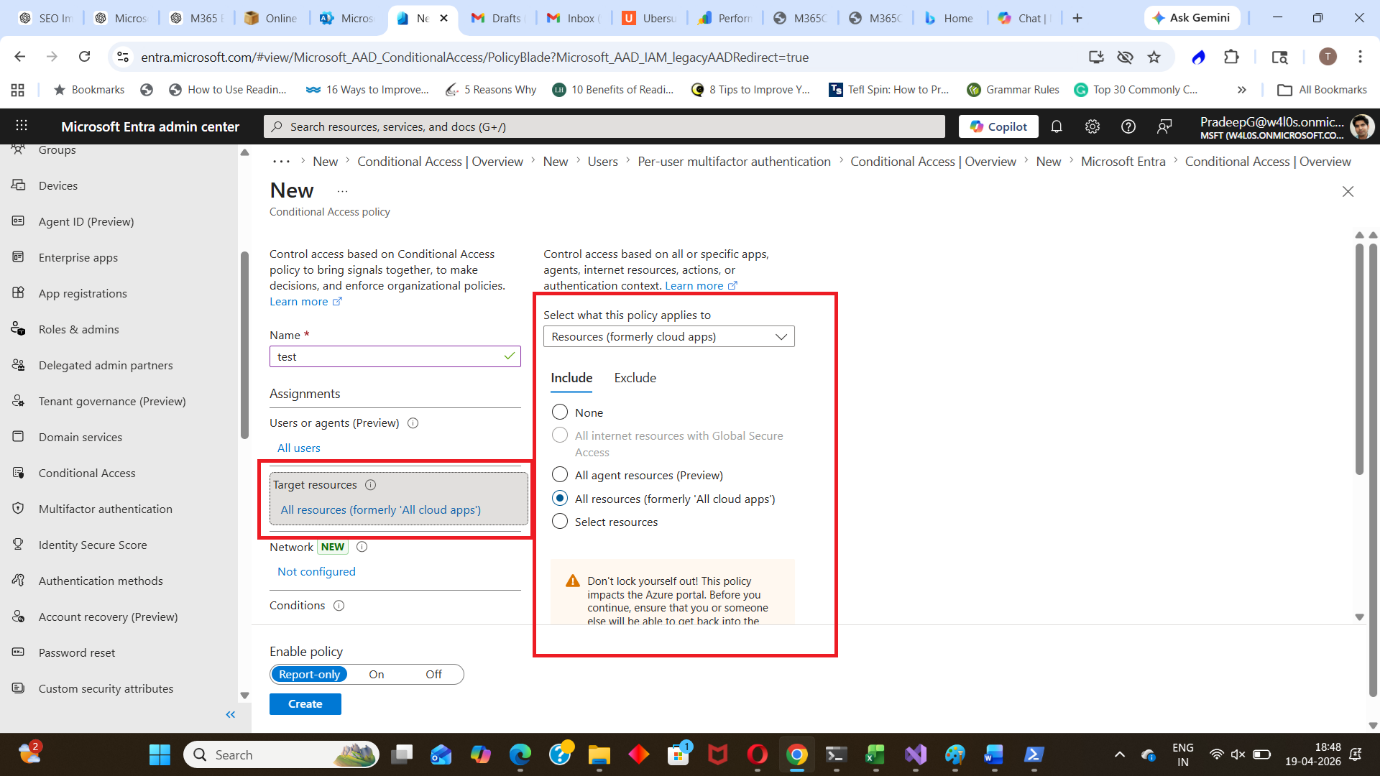
- All cloud apps
or - Specific applications
- Locations (e.g., outside corporate network)
- Device platforms
- Sign-in risk
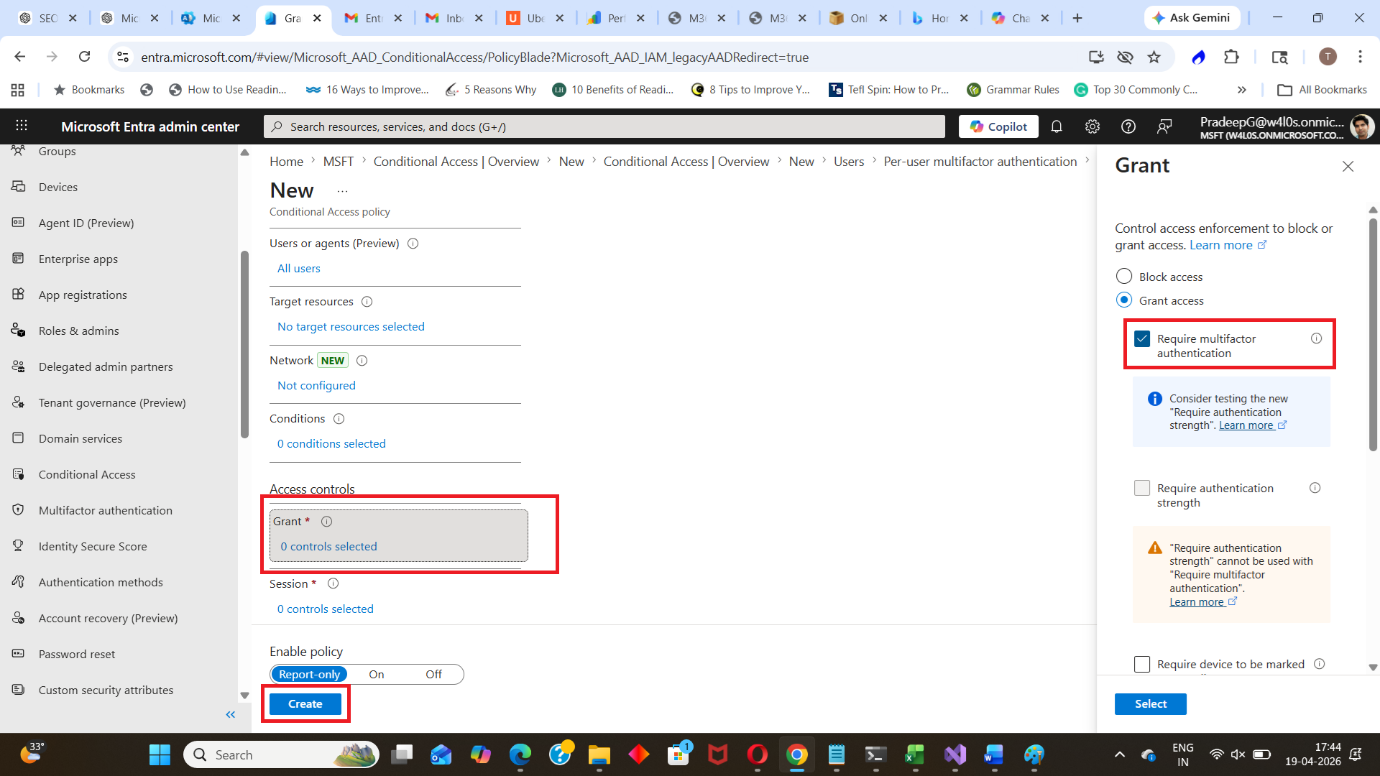
- Configure Access Controls
- Require compliant device
- Block access
- Enable the policy. Set Enable policy to: On or Report-only (recommended for testing)
- Click Create. The Conditional Access policy is now active.
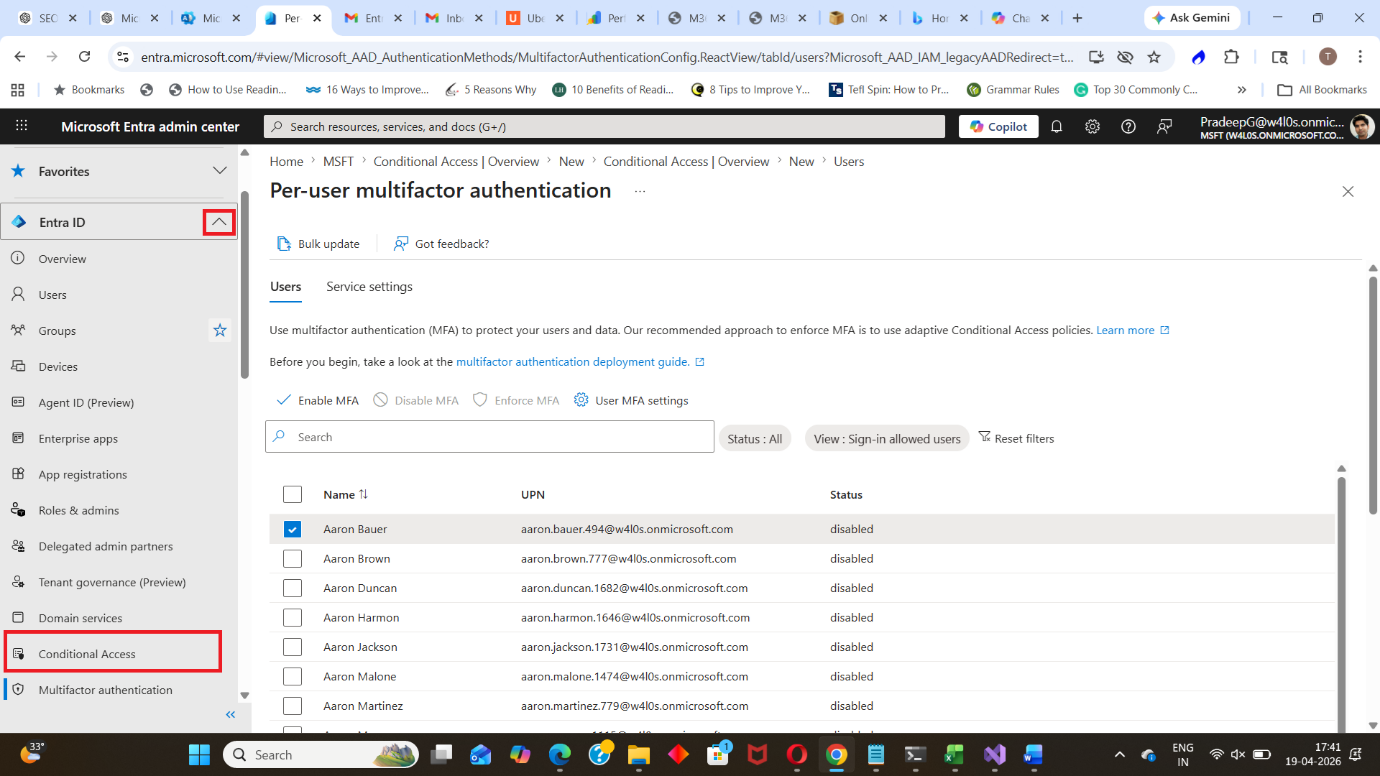
Users
Select:
Target resources (Cloud apps)
Select:
Conditions (Optional)
Configure conditions such as:
Under Grant, select:
✔ Require multi-factor authentication
or other controls like:
Create a Conditional Access Policy Using Microsoft Graph PowerShell
Conditional Access policies can also be created using Graph PowerShell.
Step 1: Connect to Graph
Connect-MgGraph -Scopes "Policy.ReadWrite.ConditionalAccess"Step 2: Create Policy (Simplified Example)
$params = @{
displayName = "Require MFA for All Users"
state = "enabled"
conditions = @{
users = @{
includeUsers = @("All")
}
applications = @{
includeApplications = @("All")
}
}
grantControls = @{
operator = "OR"
builtInControls = @("mfa")
}
}
New-MgIdentityConditionalAccessPolicy -BodyParameter $params
⚠️ Note: Real-world policies may require more detailed configuration.
Key Components of a Conditional Access Policy
| Component | Description |
| Assignments | Defines users, groups, and applications |
| Conditions | Defines when the policy applies |
| Access Controls | Defines what actions to enforce |
| Policy State | Enabled, disabled, or report-only |
Common Use Cases
Administrators create Conditional Access policies to:
- Enforce MFA for all users
- Block access from risky locations
- Allow access only from compliant devices
- Protect sensitive applications
- Implement Zero Trust security
Best Practices
- Start with Report-only mode before enabling
- Avoid applying policies to all users immediately
- Always exclude at least one emergency admin account
- Test policies with a small group first
- Combine with sign-in risk and device compliance policies
Conclusion
Creating Conditional Access policies in Microsoft Entra allows administrators to secure access dynamically based on conditions.
Using the Entra Admin Center for ease or Graph PowerShell for automation, organizations can implement strong security controls while maintaining flexibility.
Did You Know? Managing Microsoft 365 applications is even easier with automation. Try our Graph PowerShell scripts to automate tasks like generating reports, cleaning up inactive Teams, or assigning licenses efficiently.
Ready to get the most out of Microsoft 365 tools? Explore our free Microsoft 365 administration tools to simplify your administrative tasks and boost productivity.